Best MCP Registries in 2026: Compared for Developers and Enterprises
.webp)
Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
A few months ago, most teams viewed their MCP Servers as lightweight enhancements. You found one in GitHub, connected it to Claude Desktop or Cursor via JSON configuration file, and went on with your business. This approach was effective for a limited number of servers.
However, once you start scaling up your utilization to dozens of MCP Servers across multiple teams, each requiring separate authentication, uptime expectations, ownership, etc., you quickly run out of capacity to manage them all.
All these different teams end up with duplicate Servers, with their Credentials scattered throughout the environment, and no way to know which tools are using which Agent.
At the same time, the Model Context Protocol's rapid evolution has made it an industry-standard integration layer for agentic AI. Fast-growing support from major AI ecosystems and tens of thousands of servers has caused the MCP ecosystem to evolve much faster than the infrastructure available to support it.
This is where MCP registries come in. MCP registries serve as the integration and discovery layer for MCP servers. They vary widely in scope, from simple discovery catalogs to platforms that attempt to solve hosting, governance, and enterprise control problems.
Choosing the wrong approach can result in:
- Inefficient hosting models that contribute to higher clouds costs
- Unsecured connections between unverified servers
- Missing audit trails create compliance gaps
- Overhead of engineering may occur when manually managing infrastructure
In this guide, we analyse the best MCP Registries for 2026, looking at how they perform with respect to Discovery, Governance, Hosting and Enterprise preparedness. This will allow you to select the correct platform for setting up your AI agent infrastructure.
.webp)
What Is an MCP Registry and Why Does It Matter?
An MCP registry is a centralized catalog that keeps track of all MCP servers, their capabilities, and how to connect to them. You can think of the MCP registry as the discovery layer for your AI tools.
MCP registries are not the same as the actual servers. They store server metadata such as:
- Server descriptions and capabilities
- Connection endpoints and protocol details
- Authentication requirements
- Version and compatibility information
The actual servers exist where they have been deployed, whether locally, in the cloud, or with a third party. This distinction becomes more important as systems expand in size.
Developers can configure servers manually when there are only a few to manage. When agents multiply and tools connect to many systems at once, fragmentation issues emerge:
- Configuration drift across the team
- Duplicate servers being created
- Unclear server ownership
- Inconsistent application of security risks and policies across servers
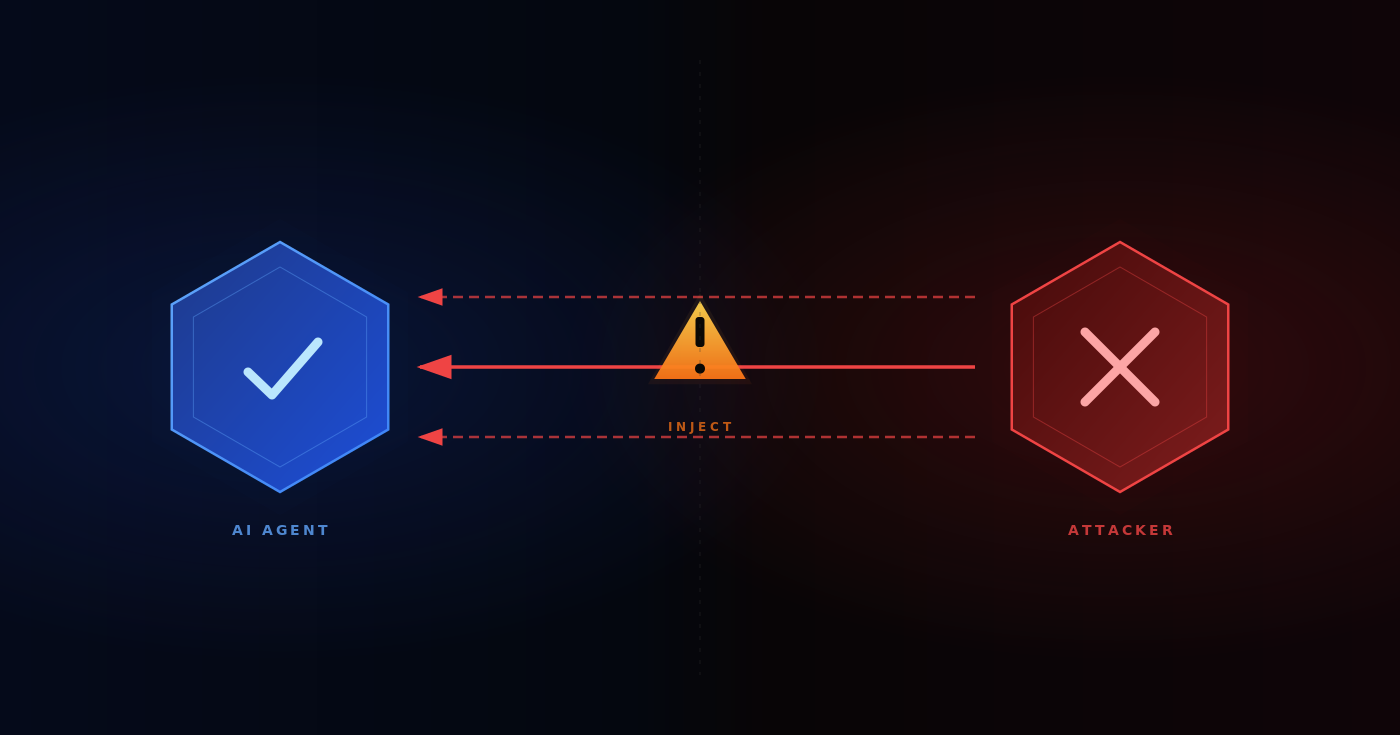
Companies are increasingly aware of this growing problem: shadow AI. Teams can connect automation agents to external tools without oversight, any way to manage these potentially dangerous data-exposure connections, or any access control.
Without a central MCP registry, there is no mechanism to track or administer these connections. The MCP registry provides the visibility and control that platform teams need before tool sprawl becomes a systemic issue.
.webp)
The Best MCP Registries in 2026
MCP Registries exist for many reasons; some include finding a server, providing a place to host an application, or managing the overall use of MCPS within the enterprise.
Below is a summary of the best MCP Registries compared based on their function and capabilities.
Official MCP Registry (registry.modelcontextprotocol.io)
A centralized repository of public metadata for MCP servers, backed by Anthropic, GitHub, PulseMCP and Microsoft. It is a METAREGISTRY—this means that while it contains metadata about packages, it does NOT contain the actual code or binaries (which live on npm, PyPI, Docker Hub; etc).
Limitation:
- Metadata only; does not provide hosting or running service;
- Still in preview and may experience breaking changes;
- Purpose-built for programmatic consumption. Not for end-user browsing;
- No built-in curation, ratings, or governance features;
Best for
- Authors of MCP Servers who want one canonical location from which to publish their Metadata; this allows all downstream registries and marketplaces to discover it.
- MCP Client Developers who want to implement discovery features through the use of the provided REST API. Enterprises needing a standardised UPSTREAM source for feeding into their own private sub-registries.
Smithery
Smithery is the closest equivalent to Docker Hub in the MCP ecosystem. This tool has over 7,000 available servers which can be either installed locally using the CLI or run on Smithery’s infrastructure as hosted remote servers. For hosted servers, Smithery will manage the runtime and provide OAuth modals for Server Authors, so they will not have to create their own authentication flow from scratch. The time from identifying your tool to getting it up and running is typically less than one minute.
Limitation:
- No enterprise governance mechanisms such as RBAC, audit logs, or approval workflows
- No visibility into security risks or token lifecycles for MCP servers
- Quality and reliability of publicly available MCP servers are inconsistent
- Not built to handle compliance needs in production environments
Best for:
Developers or small teams that want to prototype agent workflows by enabling fast discovery and setup or conduct experiments involving MCP integrations.

Glama
Glamas is a centralized source for public MCP server metadata, maintained by Anthropic, GitHub, PulseMCP, and Microsoft, and acts as a metaregistry. It contains all of the MCP package metadata but does not store the actual source code or binary files. Source code and binary files are available in the standard repositories (NPM, PyPI, Docker Hub) and can be accessed through Linda.
Limitations:
- No source code or package saved in the Glama repository; security checks rely entirely on the corresponding package repositories.
- Still in preview with no guarantees against data resets or breaking changes before general availability.
- Designed primarily for programmatic retrieval of MCP metadata by sub-registries; not for end-user browsing.
- No built-in ratings or reviews; these are provided by downstream sub-registries.
- Does not maintain any registry for MCP clients or host applications.
Best for:
- MCP Server authors who want an easy way to publish their metadata so that all downstream registries and Marketplaces can locate it.
- MCP Client developers who are developing and implementing discovery features utilizing the REST API.
- Enterprise users that are looking for a common upstream source of MCP metadata to use as a basis for creating private sub-registries.
MCP Market
An online marketplace for MCP tools, MCPMarket.com lists over 10,000 for MCP servers across 23+ categories, including Developer Tools, API Development, Data Science & ML, and Productivity & Workflow.
This is a 'Community Curated' directory with a browsable web UI that allows you to filter by category, see featured or official MCP servers, and get installation details. If you're using Cline, the install workflow is more integrated, however the directory itself is client agnostic.
Limitations:
- Third-party community directory not an official MCP project. (i.e. No namespace verification or publisher authenticated as in the case of the official MCP registry)
- No programmatic API for MCPMarket.com: It is a browsable website only (i.e. Not an API-first registry; therefore, cannot create downstream tools that interface with MCPMarket.com).
- No assurance of quality or security (in that all listings are community submitted, there appear to be no formal review processes in place).
- No one-click install from MCPMarket.com unless you are using a specific client (such as Cline).
Best for:
Developers who are interested in browsing and discovering MCP servers by category through a web UI, rather than querying an API. A useful tool for obtaining a quick visual overview of what is available within the MCP ecosystem.
MCP.so
MCP.so is a community-led directory for third-party MCP servers. It is among the biggest directories available today, with over 19,000 servers submitted. Any individual can add an entry to the directory by submitting an issue on GitHub; this is both what makes it popular and what causes it to be hard to use.
Limitation:
- Directory only; no ability to run code, no one-click install, and no programmatic API for MCP clients
- No attempt to evaluate or verify the quality or security risks of each listing; finding something suitable for production environments takes considerable effort given the volume
- No namespace ownership verification or publisher authentication
- No ratings, reviews, or usage statistics; difficult to tell which listings are abandoned
Best for:
Broad discovery if you want to see the largest selection possible of MCP servers. This can be good for gathering background information or to find obscure MCP servers that may not be listed on other curated lists.
MCP Registry Comparison Table
Let’s compare the top five MCP registries along key parameters:
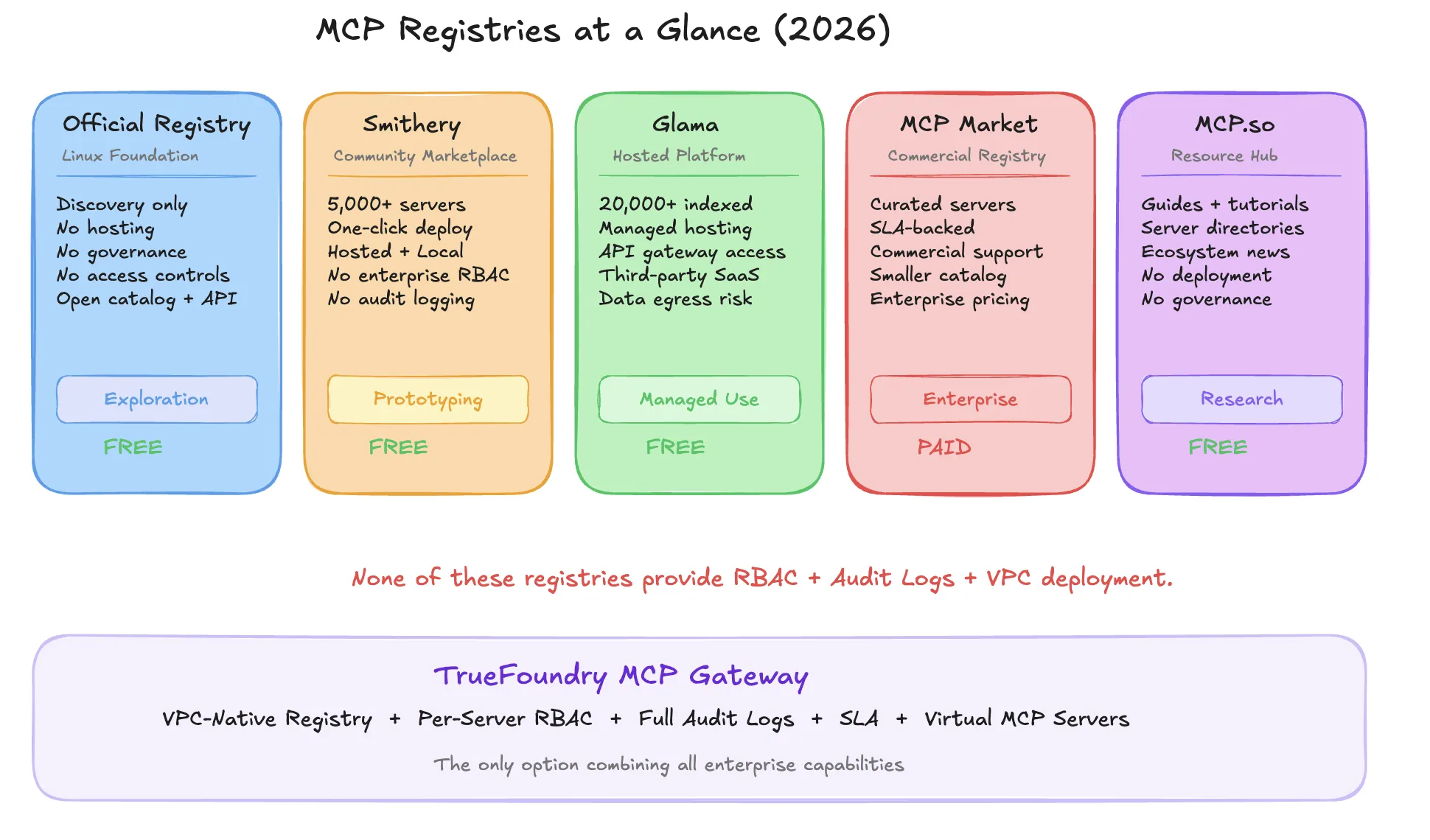
What Most Registries Cannot Do for Enterprise Teams?
The functional limitations of many MCP registries create four important gaps for enterprise-level personnel:
- Lack of server-level restrictions: Any AI agent can connect to any registered server without access control.
- No audit trail: There is no record of which agent accessed which tools, when, or what inputs were used.
- No access governance: Registries do not control user, group, or agent permission settings at the registry level.
- Data egress risk: Hosted registries route tool calls through external network infrastructure, creating compliance and security risks for organizations subject to SOC 2, GDPR, or similar frameworks.
These capabilities are not optional. They are required by any organization subject to compliance audits or operating sensitive systems in regulated industries.
.webp)
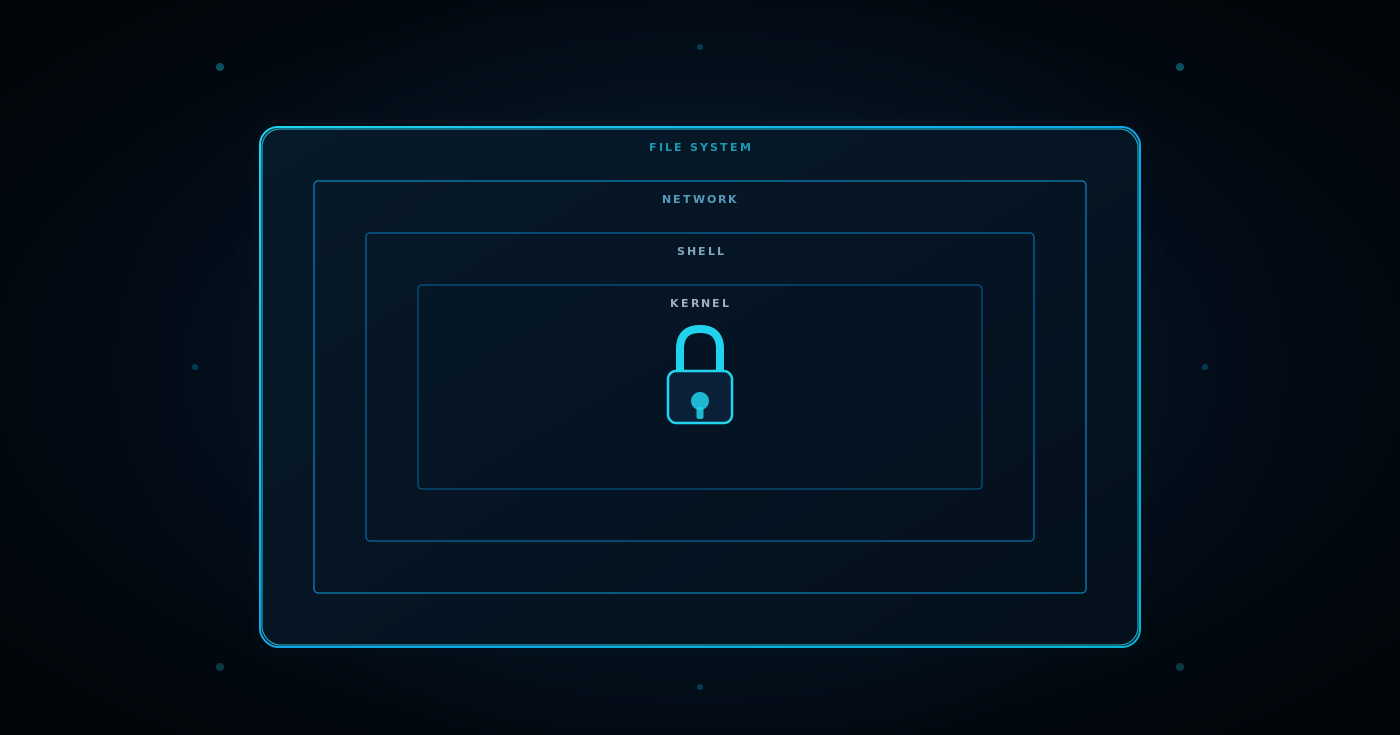
Why Enterprises Need an Internal Registry, Not Just a Public One?
Publicly available MCP servers help you determine what tools exist. Organizations must also determine who may access those tools and under what conditions. An internal registry provides three critical capabilities:
1. One Source of Information on All Public and Private Servers
Many organizations use a mix of externally-sourced and custom-developed servers to host their MCPs. The internal registry creates a centralized, controlled location for archiving both types of servers.
2. Approval Workflow Restrictions to Prevent Shadow MCP Use
Before agents can access a server, the server must be vetted so the security team can manage the agent's access.
3. Version Control and Rollback Functionality Provide Stability
Platform Managers will be able to assign and pin an agent to a specific server version and, if necessary, revert to the previous version.
Without these capabilities, organizations that adopt MCP technology at scale will face the same challenges created by earlier movements toward shadow IT. The software supply chain risks posed by ungoverned MCP servers are analogous to those posed by unmanaged traditional software components in modern software supply chains.
.webp)
.webp)
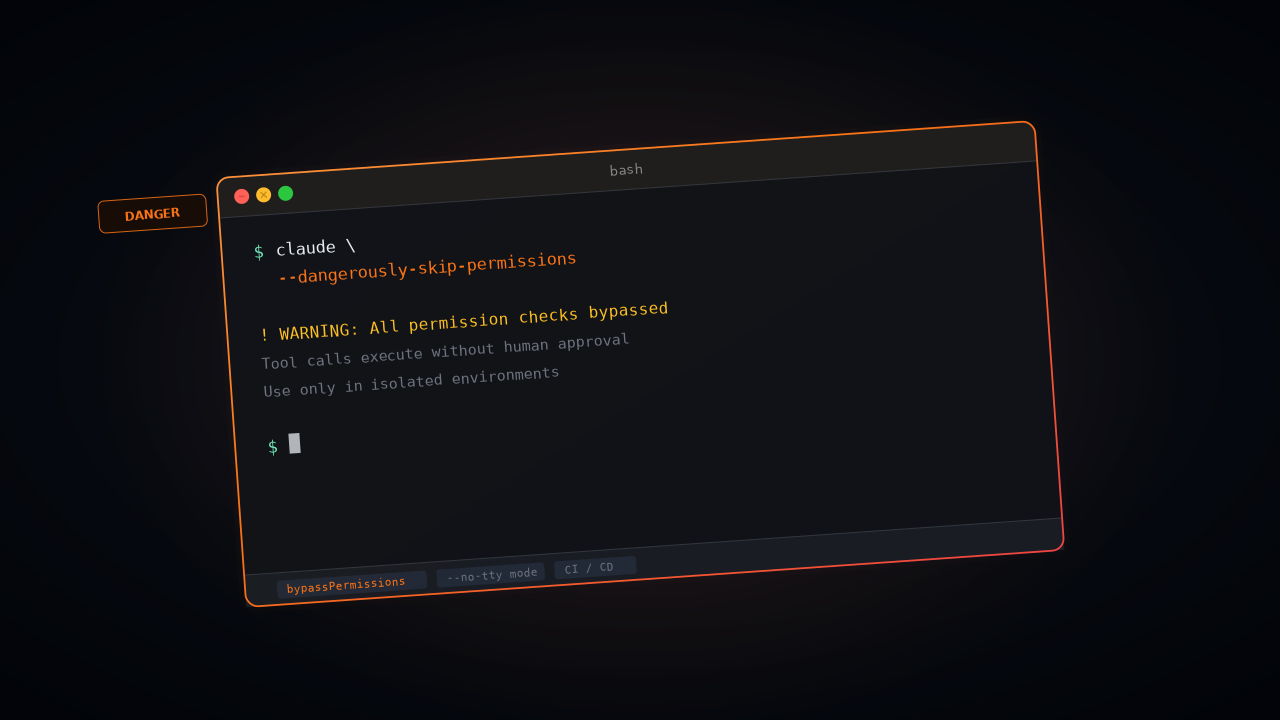
How TrueFoundry's MCP Gateway Solves What Registries Alone Cannot
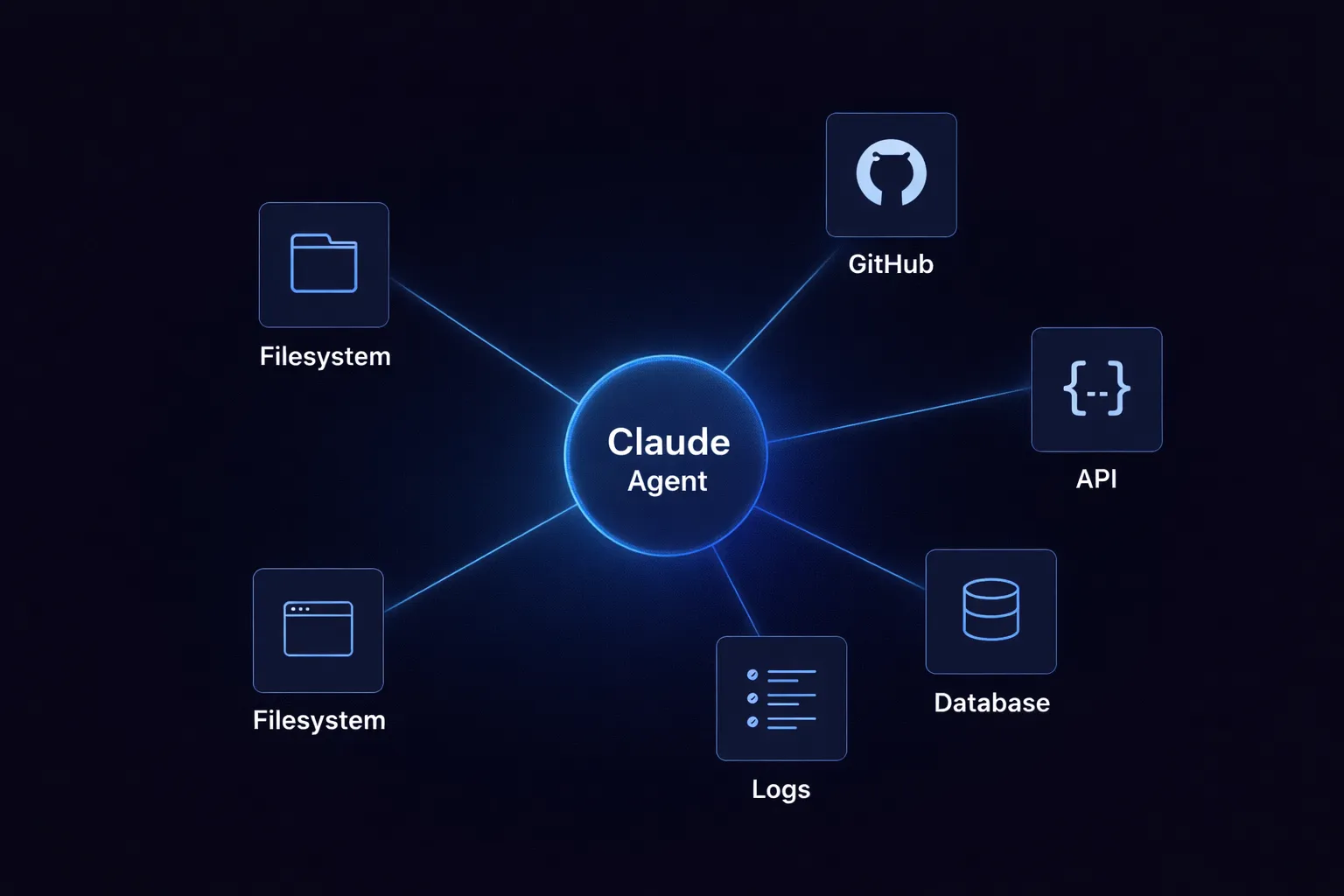
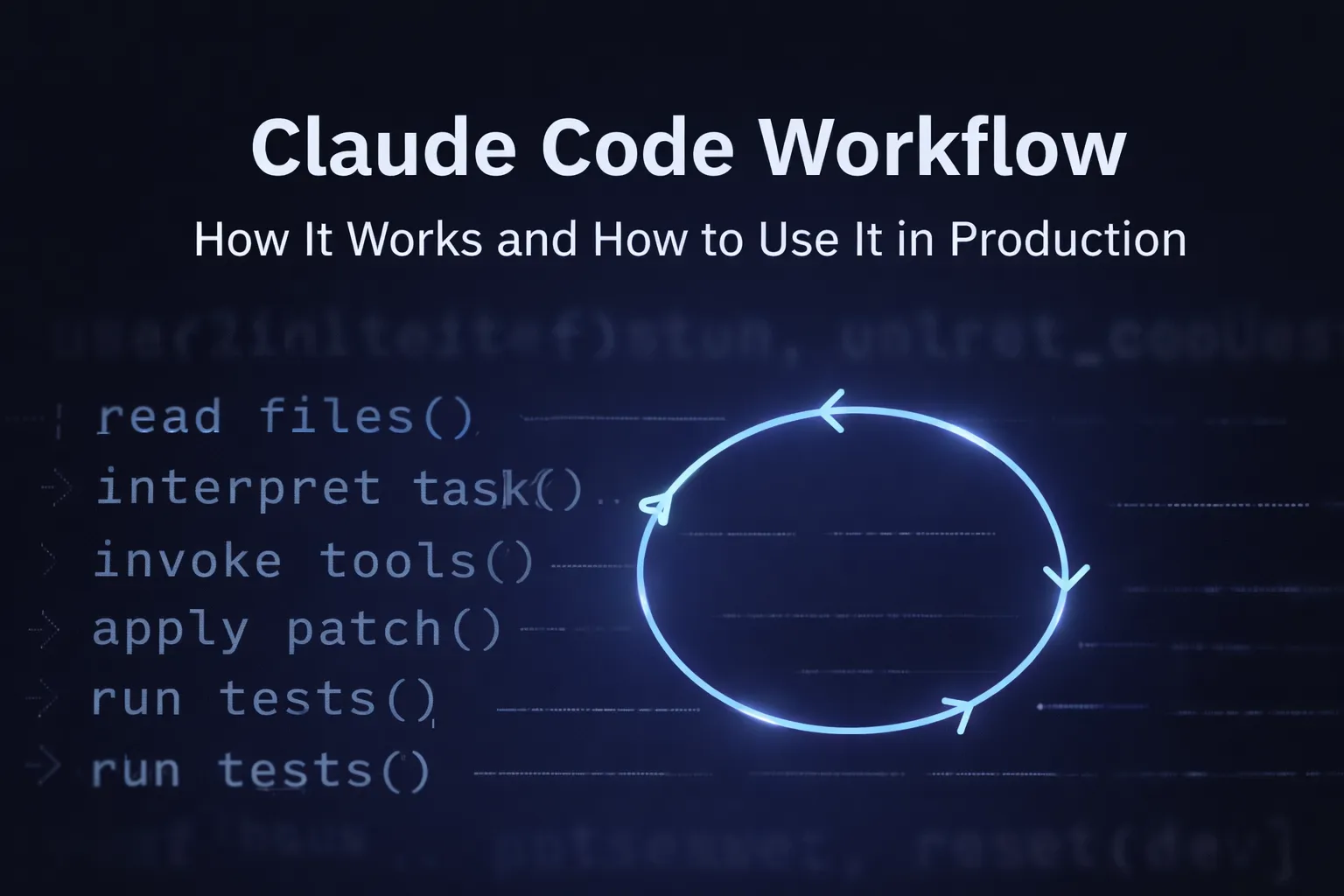
MCP registries allow agents to discover which tools exist, but they do not enforce access control, track usage, or protect sensitive systems from backend changes. TrueFoundry provides a complete control plane that extends the registry into a governed infrastructure layer.
A governed internal registry inside your own VPC
Within a control plane deployed in their own environment (AWS, GCP, Azure, or on-prem), users can register both self-hosted and public MCP server instances using TrueFoundry. All interactions will remain inside the user's network perimeter, and the agents will only be able to interact with authorized servers for teams subject to GDPR or data residency requirements; this is a must-have for control.
Granular, per-server access control
Not every agent should have access to every tool. TrueFoundry uses role-based access control (RBAC) at the server level, so each team/agent can view and invoke only the tools they are authorized to use. Platform teams define the access level a team or agent will have once and then TrueFoundry will enforce that across all access to the tool.
End-to-End Audit Logging with Identity Context
All tool usage is automatically captured with very detailed and structured metatag data; this includes the user who called the tool (the agent), the identity of the agent, the identity of the server that received the call, the date and time the call occurred, any input to the call and any output of the call. This provides automated audit trails that meet compliance for regulations such as SOC 2 and GDPR without requiring logging to separate infrastructure.
Virtual MCP Servers for stability and flexibility
By creating a virtual MCP Server, TrueFoundry provides an abstraction layer that allows agents to communicate with back-end services (TrueFoundry can thus accommodate changes to the services without changing the agent's logic). Consequently, this will provide organizations with consistently stable production processes, regardless of any changes made to the infrastructure behind the scenes (this invariance holds even after the infrastructure has been changed).
.webp)
Conclusion: Discovery Is Just the Starting Point
Community-based MCP registries are appropriate for experimentation and exploration. However, when organizations begin deploying MCPs into production environments, they are not sufficient for the governance and control that regulated or multi-team enterprise systems require.
As an organization scales its use of MCPs, common challenges emerge: limited visibility into tool usage, uncontrolled access to external services, fragmented credential management, and software delivery pipelines that lack policy checks. Without a governed internal layer, these issues can quickly become compliance and security liabilities. The risks mirror those seen with shadow AI in earlier waves of ungoverned technology adoption.
TrueFoundry enables organizations to move beyond a simple MCP registry by providing a control plane that includes server discovery, access control, audit logging, and VPC-native deployment on a single platform. This gives MCP adopters a solid foundation for reliably running MCP infrastructure in production environments.
Frequently Asked Questions
What is an MCP registry and how does it work?
An MCP registry is a centralized catalog of MCP servers storing server metadata about tools dynamically discoverable by agents. Your agents can discover tools without hardcoding them into your configuration. Registries track capabilities, connection endpoints, and authentication requirements, acting as the discovery layer for the MCP ecosystem across development teams and production environments.
What is the difference between an MCP registry and an MCP gateway?
The MCP registry is a discovery mechanism for the tools and resources available in the MCP ecosystem. The MCP gateway acts as the enforcement mechanism. The registry lists the tools; the gateway controls who has access control, how requests are routed, and how they are logged. Both are necessary for governed enterprise deployments.
Can I use a public MCP registry like Smithery in a production enterprise environment?
Publicly available MCP servers and public MCP registries work well for discovery and prototyping. However, they lack the institutional governance, access control, and audit logging needed to protect sensitive data and sensitive systems in production environments subject to compliance requirements.
How do enterprises manage access control for MCP servers at scale?
Publicly available MCP servers and public MCP registries work well for discovery and prototyping. However, they lack the institutional governance, access control, and audit logging needed to protect sensitive data and sensitive systems in production environments subject to compliance requirements.
What should I look for in an enterprise MCP registry in 2026?
Enterprises typically combine a MCP gateway, role-based access control, approval workflows, and centralized authentication to govern which automation agents can access which tools. This control plane approach prevents unauthorized automation workflows and creates the audit trails needed for compliance verification.
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.









.webp)
.webp)
.webp)

.webp)











