Best MCP Security Tools in 2026: Compared for Security Teams and Enterprises
Updated: April 11, 2026
.webp)
Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
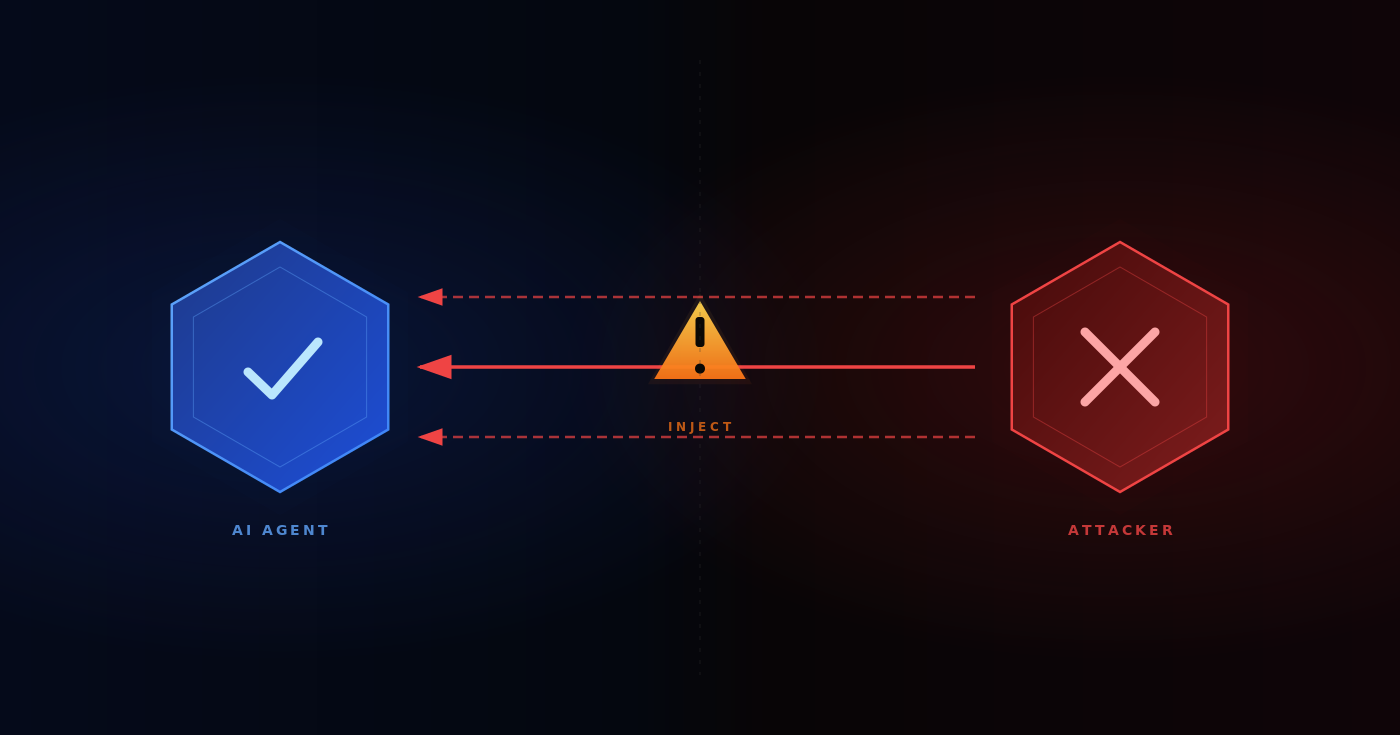
When an AI agent reads a malicious GitHub issue and immediately uses its connected credentials to pull data from private repositories, that is not a theoretical risk. Invariant Labs documented this exact attack pattern against the official GitHub MCP server in 2025.
This is how these issues appear in practice. They do not start as obvious failures. They happen quietly, often before security teams have put proper controls in place.
.webp)
The Model Context Protocol makes it easy to connect AI agents to tools by standardizing how those interactions work. That simplicity is useful, but it also introduces a new attack vector that traditional API gateways were never designed to handle.
You now have to deal with prompt injection, tool poisoning, credential sprawl, and AI agents calling external tools without clear boundaries. These are no longer rare edge cases. They are part of running production systems in enterprise environments.
This guide compares the best MCP security tools in 2026. We focus on what each tool actually does, where it falls short, and why enterprise security teams are moving toward a more centralized approach to MCP security, with platforms like TrueFoundry bringing identity, access control, and audit into a single control plane.
Your AI Agents Are Already Acting on Real Infrastructure — Is Access Controlled?
- TrueFoundry enforces OAuth-based identity injection, per-tool RBAC, and immutable audit logs across MCP servers
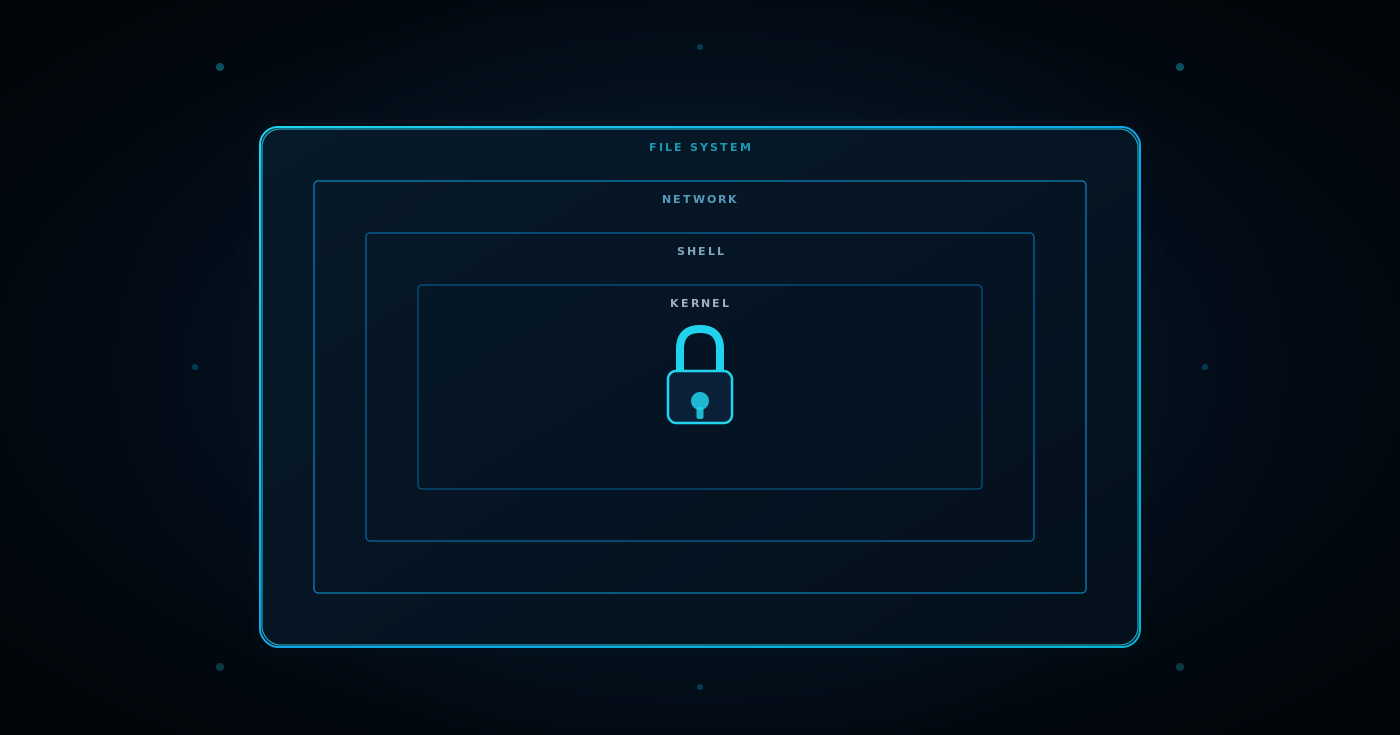
What Makes MCP Security Different From Traditional API Security
In a typical API setup, a request flows from a client to a service. You inspect the request, apply policies, and return a response.
With MCP, that model changes.
A single AI agent task can trigger API calls to 10 or 20 different MCP tools. These calls are not always visible upfront. They are generated as the agent works through a task. Traditional gateways were not built to track or control this kind of behavior across MCP traffic.
There is also a second layer of risk.
Tool descriptions themselves can be manipulated. In a tool poisoning scenario, instructions are hidden inside tool metadata. The model sees them. The human reviewing the configuration often does not. That creates a gap between what you think the tool does and what the agent actually executes. This is precisely how rug pull attacks operate in the MCP ecosystem.
Session behavior introduces another problem.
AI agents operate over longer sessions. They authenticate once and continue working. But permissions can change during that time. If the system does not re-check authorization during execution, the agent can keep operating with unauthorized access it should no longer have. This is one of the most significant security risks in remote MCP servers today.
At this point, the problem is no longer just about securing requests. You are securing intelligent systems that make decisions and act on them across external services.
.webp)
The Best MCP Security Tools in 2026
The tools below approach MCP security from different angles. Some focus on routing and policy enforcement, others on credentials or monitoring. The differences matter depending on how your system is designed and where your MCP risks are concentrated.
MCP Manager
MCP Manager is a dedicated MCP gateway. It sits between AI agents and MCP tools, routing MCP traffic through a proxy where policies are enforced before requests reach external systems. This includes rate limiting on tool invocations to prevent runaway agent behavior.
• Limitation: MCP Manager provides strong governance features such as RBAC, audit logging, and policy enforcement. However, it operates primarily at the MCP gateway layer, which means organizations still need to integrate it with separate systems for model serving, orchestration, and broader AI observability to achieve full platform coverage.
• Best for: Teams seeking a focused MCP gateway with strong enforcement who can separately manage the rest of the stack.
Lasso Security
Lasso Security is an LLM security platform that launched MCP Secure Gateway in 2025. It monitors MCP connection interactions and detects unsafe behavior at runtime using behavioral analysis across the MCP client.
• Limitation: The MCP gateway is part of a broader LLM security platform. Teams looking for deep MCP security tool governance may find that some capabilities are designed as extensions rather than core infrastructure.
• Best for: Organizations already using Lasso for AI security tools coverage who want to extend that protection to MCP without deploying another standalone tool.
Peta
Peta focuses on agent credential access. Instead of raw API keys, it issues scoped, time-limited tokens for each operation, applying the principle of least privilege at the credential level.
• Limitation: Peta provides strong credential isolation, RBAC configuration, and automatic logging of tool interactions. However, its primary focus remains credential security and approval workflows. Teams may still require additional layers to achieve full coordination across identity, access control, and runtime enforcement for local MCP servers.
• Best for: Teams concerned about credential exposure, especially where human approval is required for unauthorized actions involving sensitive data.
IBM ContextForge
IBM ContextForge is an open-source MCP gateway, registry, and proxy designed for complex, distributed environments. It goes beyond basic context protocol handling by supporting HTTP, JSON-RPC, WebSocket, SSE, stdio, and streamable HTTP, while also integrating REST and gRPC APIs into a unified control layer.
ContextForge includes a full admin interface, OpenTelemetry-based observability, Redis-backed caching, and multi-cluster federation. It also supports A2A (agent-to-agent) systems and plugin extensibility, positioning it as an orchestration and governance layer rather than just a transport proxy across MCP components.
• Limitation: ContextForge is backed by IBM but released as an open-source component with no official commercial support. Organizations must take responsibility for deployment, scaling, and operational reliability in production systems.
• Best for: Platform engineering teams that want deep control, extensibility, and the ability to build a fully customized MCP infrastructure.
MintMCP
MintMCP is a managed MCP gateway with SOC 2 Type II certification. It is designed to help teams meet compliance requirements quickly without having to build security tools from scratch.
• Limitation: As a managed SaaS platform, deployment flexibility may be constrained for organizations with strict data loss prevention requirements or VPC isolation needs around sensitive data protection.
• Best for: Compliance-driven teams that need audited controls and fast deployment without building internal infrastructure.
| Tool | Prompt Injection Protection | RBAC / Access Control | Audit Logging | Deployment Model | Coverage Scope |
|---|---|---|---|---|---|
| TrueFoundry MCP Gateway | Supported (guardrails + policy enforcement) | Supported (per-tool RBAC, identity-based access) | Supported (structured, centralized logs) | In-VPC (AWS, GCP, Azure) | Identity, access control, audit, orchestration |
| MCP Manager | Supported (policy enforcement layer) | Supported (RBAC) | Supported (traceable audit logs) | Self-hosted / VPC | MCP gateway + governance |
| Lasso Security | Supported (runtime monitoring, detection) | Supported (access policies) | Supported (interaction monitoring logs) | SaaS / Hybrid | LLM security + MCP gateway |
| Peta | Supported (input control + scoped execution) | Supported (RBAC + token scoping) | Supported (automatic tool call logging) | SaaS / Proxy-based | Credential security + access control |
| IBM ContextForge | Supported (extensible via policies) | Supported (configurable via platform) | Supported (OpenTelemetry integration) | Self-hosted (no managed support) | Full MCP platform (gateway, registry, orchestration) |
| MintMCP | Supported (policy enforcement) | Supported (access control) | Supported (audit logging) | Managed SaaS | MCP gateway + compliance controls |
| Lunar.dev MCPX | Supported | Supported (granular tool-level RBAC) | Supported | Enterprise / Hybrid | Enterprise MCP governance |
| Docker MCP Gateway | Supported (used in mitigation patterns) | Supported (via container and policy controls) | Supported (integrated logging) | Self-hosted | Container-native MCP gateway |
| Composio | Supported | Supported | Supported | SaaS / Platform | MCP integration + workflow automation |
| Bifrost | Supported | Supported | Supported | Enterprise / Controlled environments | Compliance-focused MCP security |
Most MCP security tools provide strong capabilities within specific layers of the stack. The difference is not whether security exists, but how fragmented it becomes across identity, access, and audit as systems scale.
One Control Plane for MCP Authentication, Authorization, and Full Audit Trails
- TrueFoundry deploys inside VPC and covers identity injection, per-server RBAC, and structured logging without requiring multiple tools.
Other Notable MCP Security Tools
Several tools consistently appear in enterprise evaluations and independent comparisons for MCP security coverage.
- Lunar.dev MCPX: Often positioned as an enterprise-grade MCP gateway with strong emphasis on granular, tool-level RBAC and MCP traffic governance across distributed environments.
- Docker MCP Gateway: Widely referenced in real-world security research discussions, including mitigation strategies for MCP risks. Its strength lies in integration with container-based workflows and preventing malicious code execution at the container boundary.
- Composio: One of the most widely adopted MCP integration platforms for production teams, focused on simplifying MCP tools connectivity and scaling agent integrations across data sources.
- Bifrost: Frequently evaluated in regulated environments where compliance, controlled access control, and internal system security are critical for sensitive data handling.
What Most MCP Security Tools Do Not Cover End-to-End
Most MCP security tools provide strong capabilities within specific layers of the stack, but rarely deliver coordinated control across identity, access, and runtime behavior.
The gaps tend to appear in the same places:
- Limited context inspection: If the security layer only operates at the transport level, prompt injection attacks and tool poisoning can still reach the agent because the system is not inspecting what enters the the agent context through natural language inputs from data sources.
- Fragmented security coverage: Some tools focus on credentials, others on access control or monitoring. Very few combine all three in a single system, which leads to gaps between layers and increases security vulnerabilities across MCP components.
- Deployment constraints in regulated environments: SaaS-based security platforms may require traffic to pass through external infrastructure. For regulated teams, this creates a data exfiltration risk where tool inputs and outputs leave the controlled environment, exposing SSH keys and other sensitive data.
- Incomplete audit visibility: To understand what an agent actually did, you need to correlate identity, tool calls via API calls, and outputs in real time. When logs are split across systems, you do not get a complete picture without building additional integrations, complicating incident response significantly.
.webp)
How TrueFoundry Delivers Comprehensive MCP Security
TrueFoundry approaches MCP security as part of a broader platform, rather than treating it as an isolated layer. Instead of introducing another standalone gateway, it integrates identity, access control, and audit into a single control plane that governs the full MCP ecosystem.
- In-VPC Deployment: The MCP gateway runs inside your AWS, GCP, or Azure environment, so your data, prompts, and tool descriptions stay within your infrastructure. This eliminates data exfiltration risk and satisfies sensitive data protection requirements for regulated industries.
- Native Identity Integration: AI agents inherit permissions directly from your identity provider, ensuring access control is tied to the user rather than just the system. This closes the gap that leads to unauthorized access via over-permissioned MCP client configurations.
- Built-in Guardrails and RBAC: Access control policies, PII controls, and prompt injection protections are applied at the platform level without requiring additional security tools. This enforces the principle of least privilege across every MCP connection and prevents false positives from blocking legitimate agent behavior.
- Centralized Audit Trails: Every specific action is logged with structured metadata in real time, making it easier to trace and understand agent behavior for incident response. This also provides the supply chain visibility needed to detect malicious code introductions at the tool level.
This reduces the need to combine multiple tools just to achieve baseline MCP security coverage, giving security teams a unified view of MCP traffic across large language models and connected external systems.
Frequently Asked Questions
What are the most popular MCP security tools?
The most widely used security tools of this kind in 2026 include TrueFoundry MCP Gateway, MCP Manager, Lasso Security, Peta, IBM ContextForge, MintMCP, and platforms such as Lunar MCPX, Composio, and Bifrost. Each addresses specific security risks including prompt injection, data exfiltration, and unauthorized access. Enterprise teams increasingly prefer centralized platforms that unify identity, access control, and audit in one place.
What are MCP security tools?
These MCP security tools are systems designed to control how AI agents interact with external tools through the Model Context Protocol. Unlike traditional API security, they operate at the level of agent behavior. This includes enforcing identity, validating tool descriptions, controlling permissions, and logging every action. In short, they secure not just the MCP connection, but the decisions made through it.
What is an example of an MCP security tool?
These MCP security tools are systems designed to control how AI agents interact with external tools through the Model Context Protocol. Unlike traditional API security, they operate at the level of agent behavior. This includes enforcing identity, validating tool descriptions, controlling permissions, and logging every action. In short, they secure not just the MCP connection, but the decisions made through it.
What is the difference between an MCP gateway and an MCP security tool?
An MCP gateway focuses on routing and controlling MCP traffic between AI agents and MCP tools. A full security platform goes further. It integrates identity, access control, policy enforcement, and audit logging into that gateway layer. In practice, the gateway is one component. The security platform is the system that gives it context, control, and traceability across MCP components.
How do MCP security tools protect against prompt injection and tool poisoning?
They work by inspecting both inputs and context before execution. This includes validating tool descriptions, filtering prompt injection attempts, and enforcing policies on how natural language prompts are interpreted and acted upon. More advanced security tool platforms also apply guardrails during runtime, ensuring that even if an AI agent encounters unsafe instructions, it cannot execute unauthorized actions outside its defined permissions.
Can existing API security tools protect against MCP-specific threats?
Not fully. Traditional API security tools are designed around request-response patterns. MCP security introduces a different model in which AI agents make decisions, chain API calls, and interact with MCP tools over extended sessions. Threats like prompt injection attacks and tool poisoning operate at a semantic level rather than just a network level, leaving critical security vulnerabilities unaddressed without MCP security tools.
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.
The fastest way to build, govern and scale your AI

Govern, Deploy and Trace AI in Your Own Infrastructure
Book a 30-min with our AI expert
The fastest way to build, govern and scale your AI
Book DemoRecent Blogs

The Real Cost of Generative AI — What Gartner® Research Reveals About Enterprise Mistakes
Rhea Jain
Claude Code Sandboxing: How to Isolate, Constrain, and Secure Claude Code in Production
Ashish Dubey
Prompt Injection and AI Agent Security Risks: How Attacks Work Against Claude Code and How to Prevent Them
Ashish Dubey
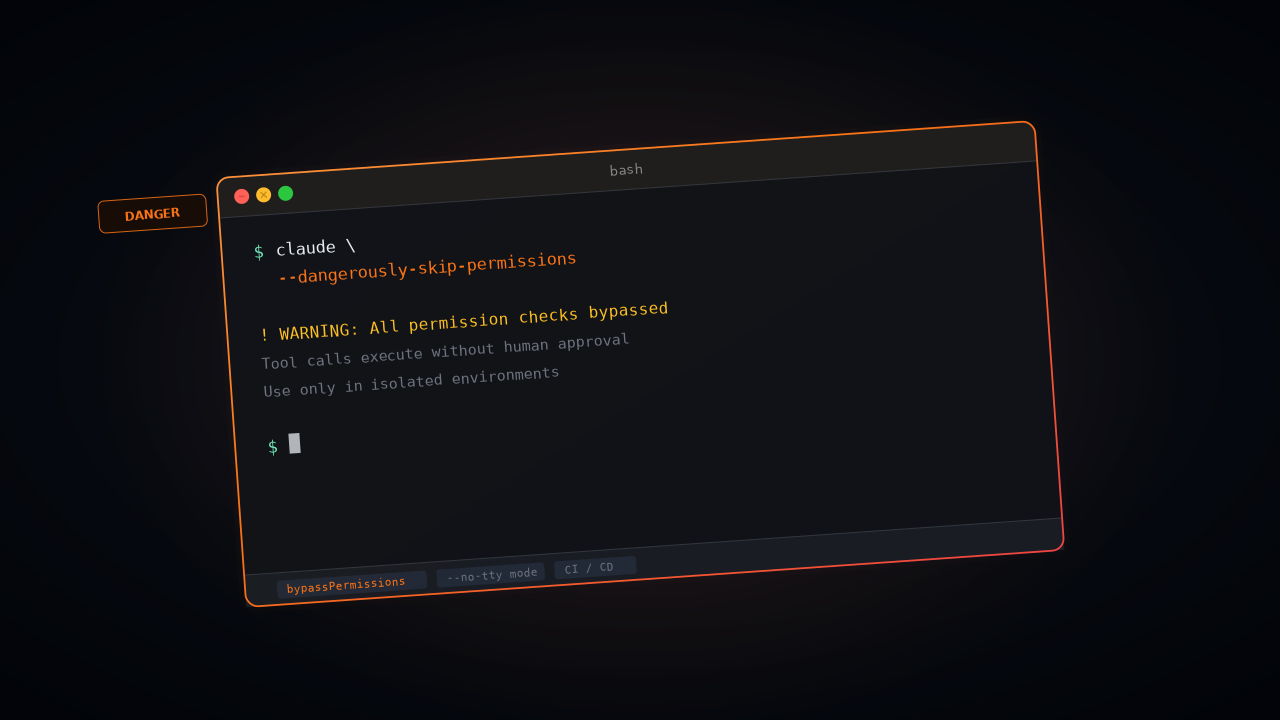
Claude Code --dangerously-skip-permissions Explained: Risks, Use Cases, and Safer Alternatives
Ashish Dubey

Stop Guessing, Start Measuring: A Systematic Prompt Enhancement Workflow for Production AI Systems


Resources




Subscribe to our newsletter
The latest news, articles, and resources sent to your inbox
















.webp)

.webp)
.webp)


.webp)
.webp)





